
The Software
KAOS
Phone-number-only authentication. Under 10 seconds to onboard. Three screens maximum. No accounts, no passwords, no friction. Your phone number is your identity. The app is free. The mesh is free. Safety should never have a paywall.
KAOS is a node-based AI threat detection platform that runs locally on every device. No cloud dependency. No central server. Every device is a node. Every node is a relay.

Zero friction
Your Phone Number Is You
No email. No password. No username. No profile photo. No social login. Just your phone number. One SMS verification code. Done. You're in the mesh — a decentralized network where every device is a node.
The device-as-identity model means your Gem IS your credential. When your phone is nearby, the Gem authenticates via BLE. When your phone is gone, the Gem continues recording autonomously and syncs when reconnected. The evidence survives even if you don't have your phone.
Why phone-number-only? Because the people who need this most — domestic violence survivors, stalking victims, vulnerable populations — are the least likely to complete a 12-step account creation flow. Every screen is a dropout. We have three screens. Total.
Node-Based Mesh Network
The Mesh: Decentralized Evidence Replication
Every device in the ReLIVE ecosystem is a node in a decentralized mesh network. Every Gem talks to every other Gem within BLE range. Evidence replicates automatically across all nearby nodes. Destroy one device — the footage already lives on every nearby device and in the cloud. The mesh uses rotating pseudonymous identifiers and Elliptic Curve Diffie-Hellman key exchange. No centralized infrastructure required.
Node Discovery
BLE scanning detects nearby nodes automatically. No pairing required. No setup. Walk near someone — you're connected to the mesh.
Automatic Replication
Evidence captured on any node replicates to every device in range. Each node relays to cloud via its companion phone. Distributed, resilient preservation.
Fear Cascade
One person's biometric distress triggers recording on every node within range. Strangers protect strangers. Automatically.
Pseudonymous Nodes
Every node rotates its identity every 15 minutes. Your Gem appears as a different device to the mesh constantly. Privacy by design.
Encrypted Node-to-Node
ECDH key exchange ensures evidence is encrypted in transit between nodes. Only the evidence owner and designated recipients can decrypt.
Offline Mesh
The mesh works without internet. Evidence caches locally on every node and syncs when connectivity returns. Works in basements, tunnels, rural areas.
Zero-Trust Architecture
Security Model
Every node in the ReLIVE mesh is cryptographically secured. A Flipper Zero can see a Gem's broadcast the way a stranger can see your house from the street. They know it's there. They can't get inside. They can't read your mail. They can't pretend to be a node in the mesh. The math won't let them.
Hardware Root of Trust
Every node in the mesh contains a hardware secure element — a tamper-resistant chip that generates and stores the node's private keys. The key never leaves the silicon. It cannot be read, copied, or extracted — even by the device's own firmware.
Physical decapping attempts trigger self-destruct. Voltage glitching is detected and blocked. The only way to compromise a node is to destroy it completely.
Perfect Forward Secrecy
Every node-to-node connection generates new ephemeral key pairs. Compromise one session — past and future traffic remains encrypted. Evidence transmitted between nodes is sealed with AES-256-GCM — the same cipher protecting classified government communications.
Even if an attacker captures years of encrypted node-to-node traffic, without the shared secret derived from ECDH, the ciphertext is indistinguishable from random noise.
Zero-Trust Mesh
No node is trusted by default. Every interaction requires mutual authentication — both nodes prove they hold valid private keys signed by ReLIVE's root certificate. A fake node broadcasting "I'm a Gem" is rejected instantly.
Commands are cryptographically signed with sequence numbers and timestamps. Replay attacks fail. Injection attacks fail. The mesh trusts math, not infrastructure.
Built on the same elliptic curve cryptography that secures Bitcoin — without the chain, the mining, or the fees. Blockchain-grade encryption. Zero blockchain overhead.
Progressive trust
Four Tiers of Trust
Trust builds over time. The mesh starts with anonymity and progresses through familiarity to full guardian access. You control every tier. The system never assumes.
Stranger
Default. Anonymous proximity detection. Pseudonymous mesh relay. No personal data exchanged.
Familiar
Repeated proximity builds familiarity score. Automatic — no action required. Enhanced mesh priority.
Trusted
Mutual opt-in. Shared location during emergencies. Named in evidence vault. Bidirectional alerts.
Guardian
Full access. Real-time location sharing. Biometric feed. Automatic emergency notification. Family tier.
Knowledge Automation Operating System
KAOS
The decentralized AI mesh network that powers everything. Stationary GPU nodes perform federated learning ("safety mining") while mobile edge nodes — your wearable devices — perform real-time inference. Hardware-agnostic. Open protocol. Governed by node operator consensus.
Seven application-layer deployments: personal safety, campus security, fleet monitoring, elder care, child safety, first responder, and smart city. One platform. Every use case.
KAOS uses Byzantine fault tolerance — if one node gets hacked or destroyed, the rest of the mesh network still agrees on what's true. No single point of failure. Safety mining rewards GPU operators with platform credits — the same economic model that powers cryptocurrency mining, redirected toward public safety.
Tamper-proof
The Evidence Vault
Every piece of evidence is cryptographically timestamped using blockchain anchoring. Content hashes are published to a distributed ledger, providing immutable chain-of-custody integrity for legal proceedings.
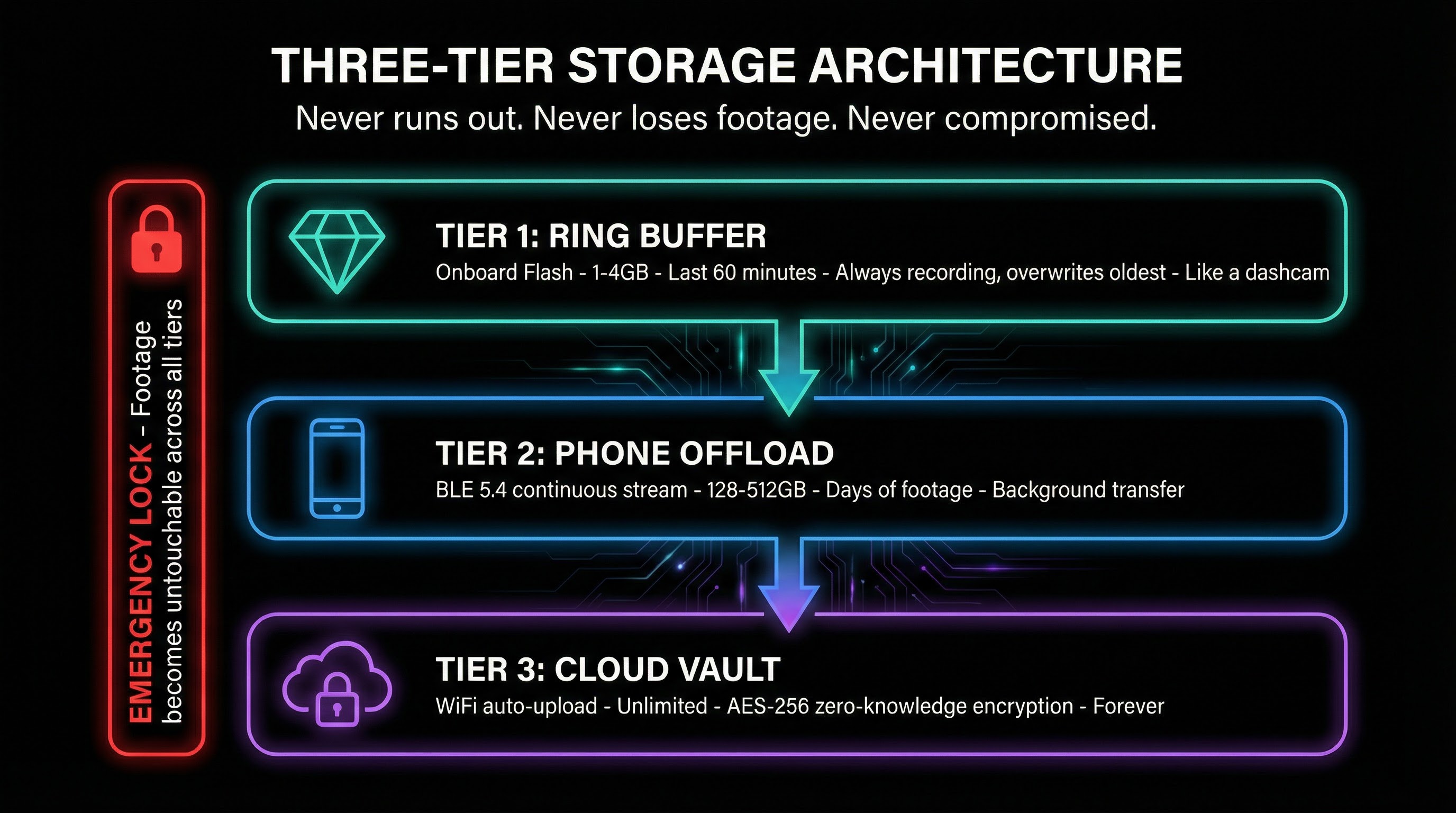
Multi-destination storage ensures evidence exists in at least three independent locations: local device, mesh relay, and cloud vault. Deletion from any single location does not affect the others. Evidence persists.
Always listening
Witness Notes
Every ReLIVE device has three MEMS microphones running 24/7. Witness Notes turns that ambient audio into searchable, timestamped transcripts — automatically. Speaker identification. Topic extraction. Action items. All on-device. All evidence-grade.
"What did the doctor say about my dosage?" "What exactly did the officer tell me?" "Did they actually agree to those terms?" Search your entire life's conversations in natural language.
Explore Witness NotesAmbient AI
Transcribing. Indexing. Sealing.
The app is free. The mesh is free. Safety should never have a paywall.
Learn why we built this.
About ReLIVE